Bottom Line: Authy delivers ironclad two-factor authentication with the best multi-device sync in the business, but its refusal to let you control your own keys makes it a deal with the devil for security purists.
The initial onboarding with Authy immediately telegraphs its philosophy. It requires a phone number. This is the root of your Authy identity, the anchor for its vaunted cloud-sync and recovery features. For the average user, this is a small price to pay for the convenience. For the privacy-conscious or those looking to minimize their digital footprint, it’s a non-starter. It intertwines an easily searchable, publicly indexed piece of data with the keys to your most secure accounts. While the security model is sound in theory, it creates a dependency that more self-contained authenticators avoid.
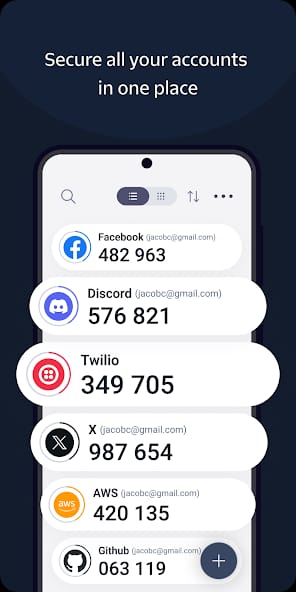
Once inside, the user experience is clean to the point of being spartan. Adding a new service is a simple matter of scanning a QR code, and your accounts are presented in a straightforward list or grid. There's no fluff, no unnecessary chrome; just your accounts and their rotating six-digit codes. It is a tool, and it behaves like one. This is where the magic of multi-device sync comes into play. Setting up Authy on a new desktop or tablet, entering your phone number, and authorizing the device is a slick process. Your full list of tokens populates almost instantly. In a world where we juggle laptops, phones, and tablets, this utility is immense. It eliminates the need to constantly reach for a single "authenticator device," a small but significant reduction in daily friction.
However, the analysis cannot end there. The core tension of using Authy revolves around its "black box" approach to your secret keys. When you scan a QR code to add a service like Gmail, you are entrusting Authy with the secret seed that generates your codes. It syncs this seed to its servers (heavily encrypted, of course) and across your devices. What it absolutely will not do is let you export that seed. This vendor lock-in is Authy's original sin. If you ever decide to switch to a different authenticator app, you cannot simply export your tokens from Authy and import them elsewhere. You must go back to every single service—your bank, your email, your crypto exchange—and manually disable and re-enable 2FA with your new app. For anyone with more than a handful of accounts, this is a monumental task. This stands in stark contrast to open-source solutions like Aegis or even Google Authenticator's more recent versions, which now allow for key export. Authy's argument is that this enhances security by preventing users from creating insecure, unencrypted backups of their keys. But it's a paternalistic security model that prioritizes the system's integrity over user agency and portability.