Bottom Line: Proton Drive stands as a bulwark against mass surveillance and data exploitation, offering unparalleled privacy in cloud storage. However, this commitment to security necessitates certain trade-offs in advanced features and raw performance, making it a specialized tool rather than a mainstream workhorse.
To truly appreciate Proton Drive, one must first calibrate their expectations. This is not the cloud storage for the casual user who prioritizes instantaneous collaboration across a sprawling software suite. No, Proton Drive is for the individual, the activist, the business, or anyone for whom data privacy is not a luxury but a fundamental right. Its architecture is a direct response to a digital world increasingly characterized by surveillance capitalism. The end-to-end encryption and zero-knowledge protocols aren't just bullet points on a marketing slide; they are the very bedrock of the service. This means that, unlike virtually every other cloud provider, Proton cannot be compelled to hand over your unencrypted data, because they simply do not possess the means to decrypt it. This is a profound distinction, and one that resonates deeply with a growing segment of the internet-savvy populace.
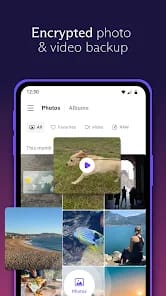
The user experience, while generally positive, reflects this security-first philosophy. The interfaces across web, desktop, and mobile are clean, intuitive, and largely free of extraneous clutter. This user-friendly approach belies the complex cryptographic gymnastics happening under the hood. For day-to-day operations—uploading, downloading, organizing files—Proton Drive functions competently. However, the friction points become apparent when one begins to compare it to its mainstream counterparts.
Where Proton Drive consciously makes concessions is in the realm of advanced features. You won't find the real-time, granular collaboration tools that define Google Docs or Microsoft 365 integration. There’s no deep, context-aware indexing for rapid searching across document content. These are sophisticated features that, in many cases, would fundamentally compromise the zero-knowledge encryption model. It’s a trade-off that Proton makes transparently, asking users to decide whether the enhanced security is worth foregoing some of the conveniences they might have grown accustomed to elsewhere.
Performance is another area where Proton Drive, while adequate, doesn't always soar. Our internal research corroborates user feedback: file synchronization and transfer speeds can occasionally be average. This isn't to say they are glacial, but in an age of gigabit internet connections, minor delays become perceptible. For large file transfers or frequent, simultaneous syncs across multiple devices, this can introduce a subtle but persistent layer of frustration. Similarly, the photo features are notably less developed than dedicated photo services. While you can store images securely, the experience lacks the intelligent organization, editing capabilities, or advanced sharing options offered by platforms like Google Photos or Apple Photos. This positions Proton Drive firmly as a secure repository, not a media management hub.
The secure sharing options, however, are a standout. The ability to apply password protection and expiration dates to shared links transforms a common vulnerability into a controlled exchange. This level of granular control over who accesses your data and for how long is an invaluable asset for professionals handling sensitive information. Furthermore, its natural integration into the Proton ecosystem is a compelling proposition. For those already invested in Proton Mail or Proton VPN, Drive provides a cohesive, end-to-end private digital experience, leveraging a single secure identity across multiple critical services. This ecosystem play creates a powerful network effect for privacy-conscious users, simplifying their digital security posture.
Security Architecture
Proton Drive's commitment to Swiss privacy laws and its open-source codebase, which has undergone multiple independent security audits, are not mere marketing buzzwords. They are foundational pillars that foster a rare degree of trust in the digital realm. In an industry plagued by opaque practices and questionable data handling, this transparency is a breath of fresh air. Users aren't just taking Proton's word for it; they can inspect the code and verify the security claims independently. This level of auditability is paramount for a service dealing with sensitive user data.