Bottom Line: Proton Mail delivers on its promise of uncompromising email privacy and security, a critical digital bulwark in an era of pervasive surveillance, though its mobile applications still contend with frustrating performance and feature parity issues.
Proton Mail is not merely an email client; it's a statement. Its very existence challenges the prevailing surveillance capitalism model that underpins much of the internet. The cornerstone of its utility lies in its end-to-end and zero-access encryption. This isn't a nebulous marketing term; it represents a fundamental architectural decision. When you send an email via Proton Mail, it's encrypted on your device, traverses Proton's secure infrastructure, and is only decrypted on the recipient's device. For communications with non-Proton users, the system ingeniously allows for password-protected encrypted messages, providing a secure, if slightly less seamless, bridge to the unencrypted world. The "zero-access" claim is equally potent: even if Proton's servers were compromised, the data stored there would remain impenetrable without the user's password, which never leaves their device. This level of intrinsic privacy by design is a rare commodity.
The significance of open-source cryptography cannot be overstated. In the opaque world of digital security, trust is paramount, and blind faith is a liability. By making its cryptographic implementations public, Proton Mail invites scrutiny from the global security community. This transparency is a potent antidote to skepticism, allowing independent verification of its claims and fostering a higher degree of confidence than proprietary, closed-source solutions can ever hope to achieve. The platform’s additional security layers—sophisticated spam filtering that actually works, robust phishing detection, and a built-in email tracker blocker—further solidify its position as a digital fortress. These aren't peripheral add-ons; they are integral components of a holistic security posture, defending against both passive data collection and active malicious attacks.
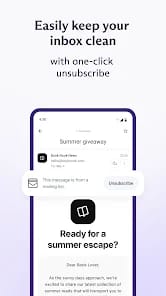
User experience, however, reveals a more nuanced picture. While the desktop web interface is generally clean and functional, facilitating efficient inbox management through custom folders, labels, and search, the transition to mobile platforms introduces friction. The promise of a "streamlined experience" on iOS and Android often bumps against the jagged edges of real-world implementation. The core functionality—sending and receiving encrypted mail—is, of course, present and secure. But the fluidity and responsiveness that users have come to expect from modern mobile applications developed by tech giants are, at times, noticeably absent. The inherent overhead of encryption, while necessary for security, can occasionally contribute to perceived latency in operations that are instantaneous in less secure environments. This is a trade-off, certainly, but one that power users will register.
The ongoing effort to achieve feature parity across platforms is also a critical point of contention. Users migrating from more mature, feature-rich email clients often find Proton Mail's mobile apps lagging behind in certain advanced functionalities they’ve grown accustomed to. This isn't a deal-breaker for the privacy-conscious, but it does mean a slight adjustment period and potentially a reduction in certain productivity workflows. The clean, minimalist aesthetic, while appreciated for its lack of clutter, sometimes veers into being too sparse, occasionally obscuring features that should be more readily accessible. Navigation, while logical, might require an extra tap or two compared to competitors, contributing to a sense of slight inefficiency for those accustomed to hyper-optimized interfaces. For a service so critical to security, ease of use is not a secondary concern; it is a vital component of adoption and consistent adherence to best practices. If a secure tool is too cumbersome, users will inevitably seek less secure but more convenient alternatives, undermining the very goal of privacy.
User Experience Flow
The process of onboarding and daily usage with Proton Mail is straightforward enough for most, but not without its quirks. Setting up a new account or migrating existing ones is generally intuitive, guided by clear instructions. Daily email composition, reading, and organization mimic standard email clients, albeit with the reassuring "encrypted" badge visible. The integration of encrypted contacts and calendar (within the broader Proton ecosystem) adds significant value, creating a cohesive, secure digital workspace. However, the search functionality, while robust on the desktop, can feel less immediate on mobile, and the synchronization of notifications, particularly on Android, has been a recurring pain point for some users. This creates an inconsistent experience that can disrupt workflow and erode confidence in the mobile app's reliability.