Bottom Line: Enpass is the definitive antidote to the subscription-heavy, server-dependent status quo of modern security tools, trading a sliver of "it just works" convenience for absolute data sovereignty.
The core of the Enpass experience is a fundamental rejection of the "silo" model. Most modern software tries to lock you into an ecosystem; Enpass tries to give you the keys to the exit.
The Sovereignty Shift
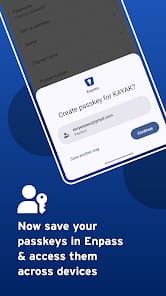
When you first set up Enpass, the onboarding friction is palpably higher than its cloud-native competitors. You aren't just creating an account; you are choosing a storage strategy. For a seasoned user, this is empowering. For a novice, it might feel like a hurdle. However, this friction is the price of sovereignty. By forcing the user to select a sync target—be it a personal Dropbox folder or a WebDAV server—Enpass ensures that you are aware of exactly where your digital life is stored. This transparency is refreshing in a market that usually tries to hide the "where" behind a curtain of marketing fluff.
Interface & Information Density
The application avoids the trap of over-simplification. While the UI is clean and follows modern design language, it doesn't sacrifice information density. With over 80 customizable templates, Enpass acknowledges that our digital lives consist of more than just usernames and passwords. It treats a government ID, a software license, or a credit card with the specific metadata fields they require, rather than forcing everything into a generic "note" box. The Password Audit tool is particularly sharp, identifying not just weak or reused passwords, but also flagging credentials that have surfaced in known data breaches. It transforms the vault from a static list into an active security monitor.
The Friction of Sync
The trade-off for this decentralized model is latency. Because Enpass relies on third-party cloud APIs for syncing, the handshake between devices isn't always as instantaneous as a proprietary server-side implementation. Occasionally, you might find yourself waiting three or four seconds for a vault to refresh after an update on another device. Furthermore, browser extensions have historically been the "Achilles' heel" of the Enpass ecosystem. While they have improved significantly, the communication between the standalone app and the browser plugin can occasionally stumble, requiring a restart of the application to re-establish the bridge.
Security Mechanics
Under the hood, the reliance on SQLCipher is a sophisticated choice. It ensures that the database is encrypted from the first byte, protecting against forensic analysis even if the underlying file is compromised. The inclusion of a built-in TOTP authenticator is more than just a convenience; it’s a workflow optimizer. By consolidating the login and the second factor into a single secure container, Enpass reduces the "device-switching" fatigue that often leads users to disable 2FA out of pure annoyance. It’s a pragmatic approach to security: make it easier to do the right thing, and people will actually do it.