Bottom Line: Jami is a uncompromising, serverless communication tool that trades the convenience of centralized clouds for absolute user privacy. It’s a powerful, if occasionally temperamental, fortress for those who refuse to let their data pass through a third-party gatekeeper.
To understand Jami, you have to understand the latency and reliability trade-offs inherent in P2P design. In a traditional app, when you send a message, the server catches it and holds it until the recipient is ready. In Jami, there is no catcher. If you send a message while the recipient is offline, the P2P handshake cannot complete. While the introduction of Swarms—Jami's decentralized group chat technology—attempts to mitigate this by syncing history across multiple peers, the fundamental "direct-to-device" requirement remains a hurdle.
The P2P Paradox
The core utility of Jami is its greatest weakness: synchronicity. During testing, the experience fluctuates between feeling like the future of the internet and a relic of the dial-up era. When both parties are online and properly indexed on the DHT, the call quality is remarkably crisp, often surpassing centralized competitors because there is no server-side throttling. The high-definition audio and video feel direct and uncompressed.
However, the "where are you?" problem is real. Because Jami doesn't use a central directory, finding your contact's current IP address via the DHT can sometimes take several seconds—or fail entirely if the network conditions are poor. This is the friction of freedom. You aren't just sending a message; you are conducting a search-and-rescue mission for your friend's digital signature across a global mesh of devices.
Interface & Flow
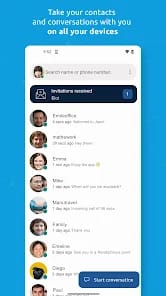
The user interface avoids the cluttered "lifestyle app" aesthetic of its peers. It is utilitarian to a fault. Onboarding is refreshingly fast precisely because it asks for nothing. You generate an ID, and you’re in. Adding contacts, however, requires the manual exchange of long alphanumeric strings or QR codes. There is no "Scan my contacts" button here—because Jami doesn't have access to your contacts, and neither does anyone else.
This onboarding friction is a feature, not a bug. It forces a deliberate hand-off of identity. Once the connection is established, the messaging flow feels familiar, supporting file sharing and screen sharing with the same P2P efficiency. But the absence of "read receipts" or "typing indicators" by default reinforces the feeling that you are shouting into a very private, very secure void.
Professional Utility
One of Jami’s most overlooked strengths is its dual identity as a SIP client. For users who need to bridge the gap between radical privacy and legacy telecommunications, this is a massive win. You can use Jami to connect to an office PBX while maintaining a separate, encrypted P2P identity for sensitive internal comms. This makes it more than just a "chat app"—it's a versatile communication terminal for the technically literate professional.