Bottom Line: Tailscale doesn't just replace the VPN; it reinvents secure network access, delivering a "Zero Trust" mesh that feels less like networking, more like magic.
The profound impact of Tailscale isn't merely in its feature list; it's in the fundamental re-architecting of how we perceive and manage network access. Traditional VPNs, for all their utility, are fundamentally flawed. They create a secure tunnel to a corporate network perimeter, then often grant broad access within that perimeter. This "moat-and-castle" approach is increasingly untenable in a world of distributed workforces, cloud-native applications, and proliferating endpoints. Tailscale's Zero Trust model surgically addresses this. Instead of trusting devices inside a network, it trusts nothing by default. Each connection attempt, from any device, is individually verified against user identity and device policies. This paradigm shift means a compromised laptop on a home network doesn't automatically grant an attacker carte blanche across your entire infrastructure.
The adoption of WireGuard is not incidental; it's foundational. WireGuard is a marvel of modern cryptography and network engineering – a lean, fast, and auditable protocol that eschews the bloat and complexity of IPSec. Its efficiency translates directly into lower latency and higher throughput, making secure connections feel indistinguishable from being on the local network. When every device in your "tailnet" can establish a direct, encrypted link to any other authorized device, the archaic concept of a central VPN server becomes largely irrelevant. This peer-to-peer mesh architecture is a revelation for multi-cloud environments, where services spanning AWS, GCP, and Azure can communicate as if they were in the same datacenter, without the need for intricate peering configurations or costly VPN gateways.
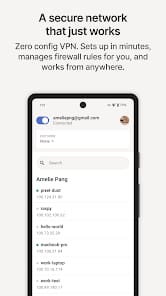
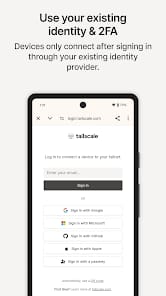
User experience, often an afterthought in network infrastructure, is where Tailscale truly differentiates itself. The "magic" users often describe isn't hyperbole; it's the sensation of complex networking vanishing. Onboarding a new laptop, server, or even an IoT device often involves little more than installing an agent and authenticating via an existing identity provider. The system dynamically assigns private IPs (often 100.x.x.x addresses), handles NAT traversal (via STUN/TURN servers), and manages DNS, all without manual intervention. This level of abstraction liberates developers and IT administrators from the Sisyphean task of network configuration, allowing them to focus on application logic and core business functions. For remote teams, the ability to seamlessly connect to internal tools, development servers, and production environments, regardless of their physical location or network topology, isn't just convenient – it’s a critical enabler of productivity and collaboration. The shift from a network-centric security model to an identity-centric one is not merely a technical upgrade; it’s a strategic advantage, allowing organizations to adapt to the fluid demands of the modern digital frontier with unprecedented agility.